IAM, AuthN & AuthZ
IAM
Enforcing least privilege
-
Access: A New Portal for Managing Internal Authorization (discord.com) A premier on authorization and access management
-
The product we ended up using should be designed to decrease risks associated with long-standing, elevated, and sometimes no-longer-needed permissions to protect our systems and customer data.
-
We wanted an intuitive user experience that didn’t require staff to have deep knowledge of the access control tool or the systems being managed. This would help ensure the tool’s adoption within the company
-
team members likely would not have enough context to make informed decisions about access and end up ‘rubber stamping’ requests. By delegating access approvals to application owners and people leads with the most understanding about the application or role and permissions being requested, we could reduce risk while distributing the load.
-
Users should be able to see what access they or their teammates have, what resources are controlled by the system, what permissions they had in the past but have since expired, and they should be able to request access to resources freely. This would empower employees to troubleshoot their own permissions and solve issues through access requests.
Fundamentals
-
AuthN & AuthZ
Kerberos
- Quick Overview of Kerberos Authentication | by Nairuz Abulhul | R3d Buck3T | Medium
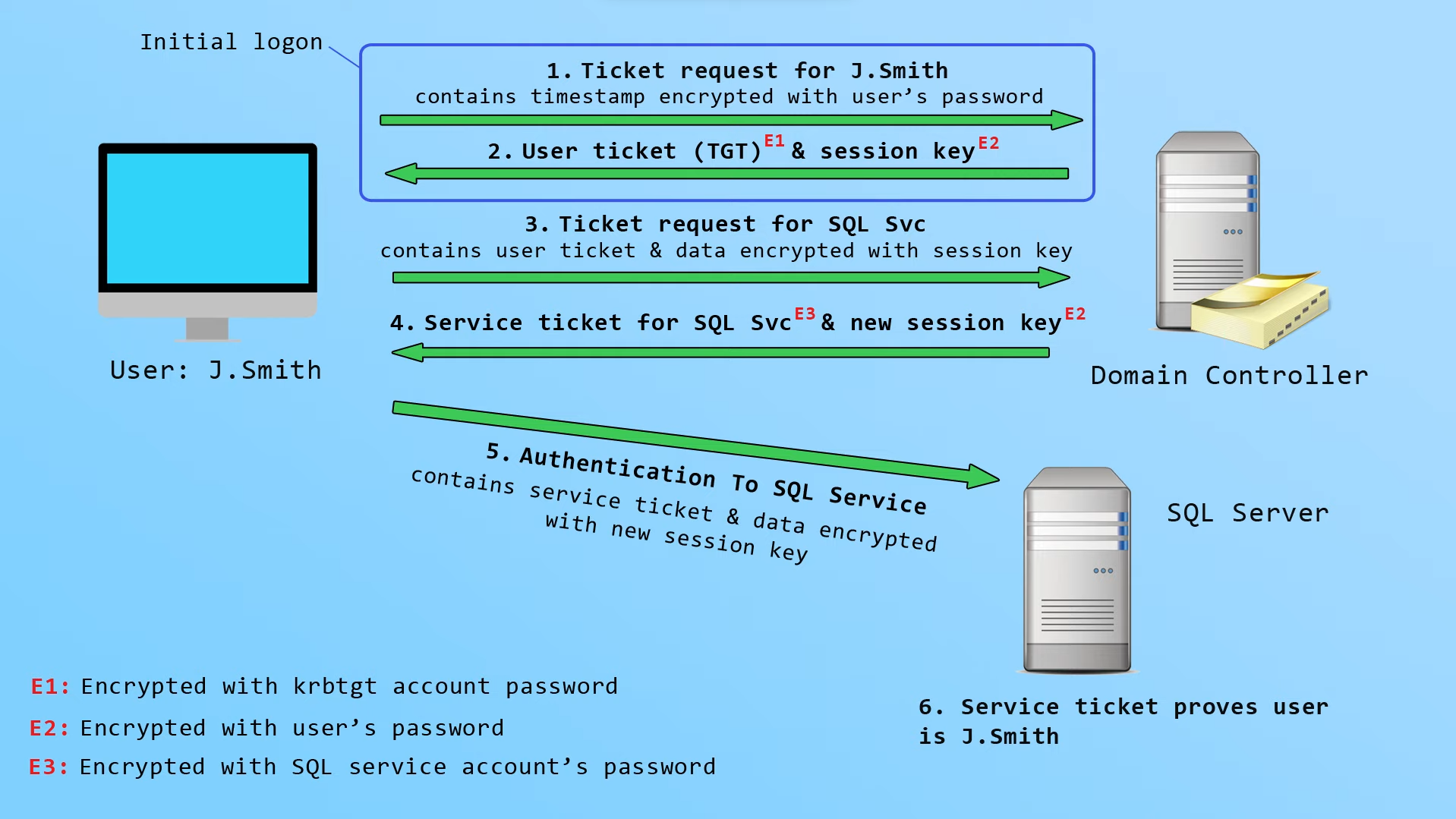
Note that the account passwords in the previous diagram refers to the NTLM hash of the user password, not the clear-text password - as those are not stored on-desk in clear-text.
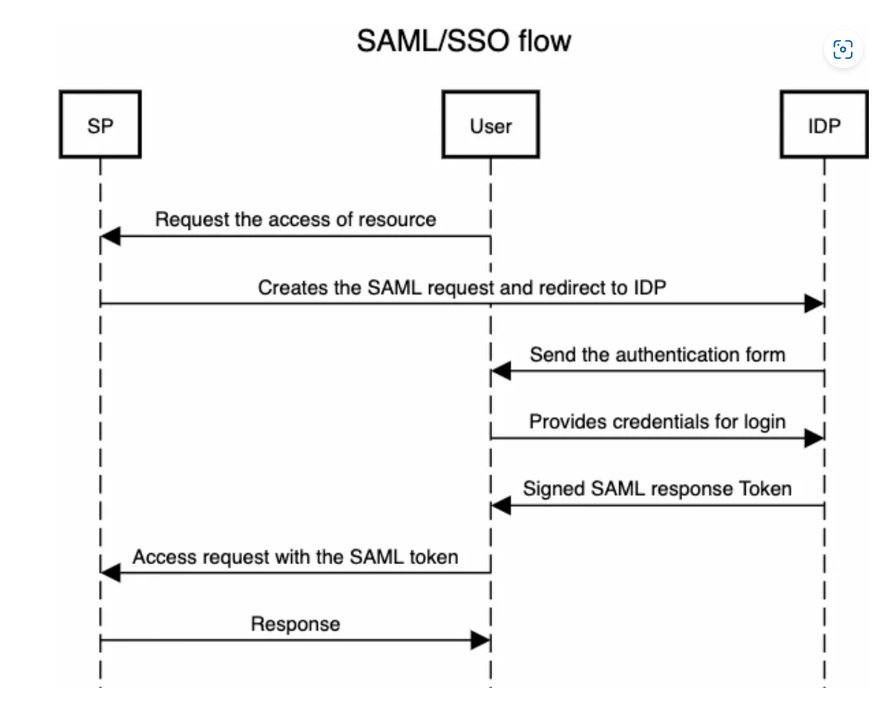
SAML
- What is SAML and how does SAML Authentication Work (auth0.com)
- SAML AuthnRequest Examples | SAMLTool.com
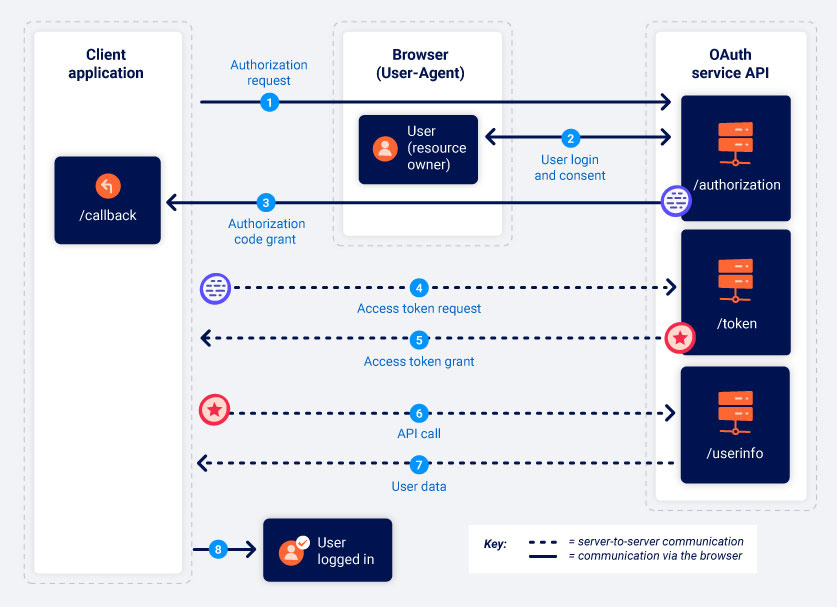
OAuth
- OAuth grant types | Web Security Academy (portswigger.net)
- What are the trade-offs between implicit grant flow and authorization code flow? (linkedin.com)
Authorization Code Grant
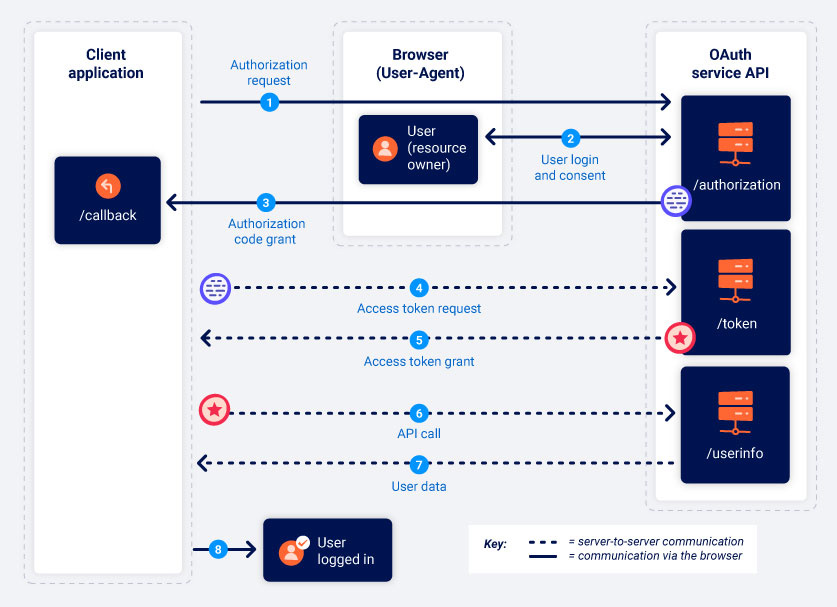
Implicit Grant